This is a multiple part series for someone new to wireless hacking, with pictures and videos.
Introduction To Kali and WiFi Pen Testing
How to Install Kali Linux
WEP Hacking
Kali Linux and Reaver
Getting a Handshake and a Data Capture, WPA Dictionary Attack
Using Aircrack and a Dictionary to Crack a WPA Data Capture
Cracking a WPA Capture with the GPU using HashCat
Creating a Dictionary / Wordlist with Crunch Part 8
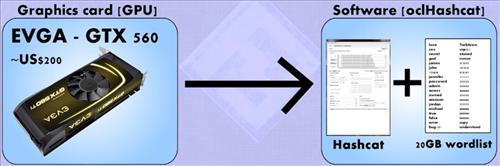
After a WPA/WPA 2 Handshake Capture has been saved to a drive cracking it with current computers can be challenging. To speed this process up the GPU in some video cards can be utilized.
This can speed things up drastically when doing a brute force crack on a WPA data capture.
You will need to know the video card you are currently using and Google it to see if it is compatible.
In the instructions before this aircrack-ng was used to show how to crack a WPA capture with a dictionary.
In this example a tool called oclHashCat will be used in order to utilize a video cards GPU.
A dictionary file and the data capture are still needed only we will be using the video cards GPU to speed up the process. Always check to see if your card is compatible and the correct drivers are loaded.
Nvidia and AMD/ATI Video cards use two separate hashcat names.
The two main versions of HashCat are:
oclHashCat for AMD/ATI graphics cards
cudaHashCat for Nvidia graphics cards
Extract it with 7z x oclHashcat-plus-0.14.7z (Don’t use 7x e as it will not preserve the directory structure.)
To use hashcat the .cap file needs to be converted to ahccap file to do this use air-crack-ng.
aircrack-ng (out.cap) -J (out.hccap)
Run hashcat against your new capture file using the correct version.
cudaHashcat-plus32.bin -m 2500 (filename).hccap (wordlist)
Your site explains thing in detail, which make me understand things better, I have been battling just to get commands to work, yours are step by step and I’m eager to try them out 🙂