Kali Linux can run on many android phones after all it is Linux which the android is also based on. The problem is the wireless chipset built into most smart phones which cannot do wireless penetration testing.
The same way in which a compatible Kali Linux USB adapter with the correct chipset is needed on a PC the same is needed with a smart phone.
There are some exceptions as several groups are working toward creating portable software and drivers for Kali. Keep in mind there currently is no app that can be simply downloaded; installed and do wireless penetration testing. Every current project requires rooting and modding an android phone.
One project called bcmon is interesting because they are coding the drivers in certain phones to take advantage of pen testing. Some smart phone’s do have the chipset required to do pen testing, but the default drivers do not take advantage of their full potential. Only some phones are capable of this.
For example, the wireless chipset in a Galaxy S1 or S2 can be used with bcmon while the newer S3, S4 and S5 do not have a chipset that will work.
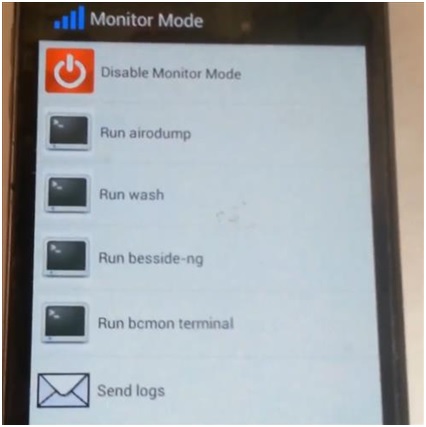
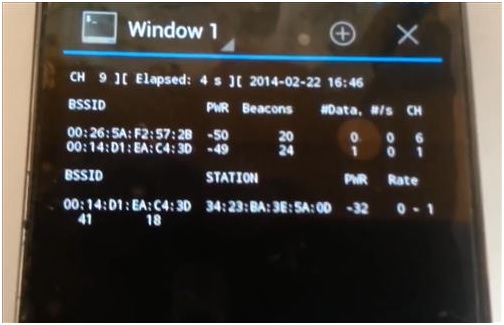
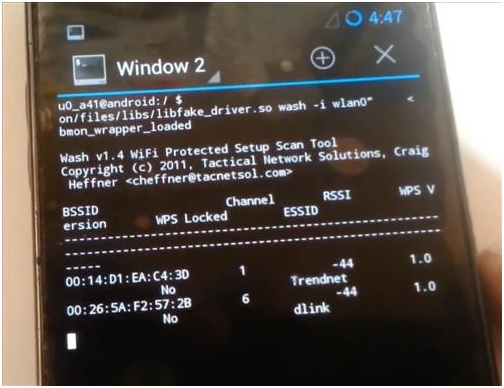
I have used bcmon on a Galaxy S2 and it did work, although all the parts combined to get it to work made it very crash prone. It requires the mod Cynagen 9 or higher on a rooted phone, and the bcmon drivers. Here are some screen shots.
This project hasn’t been updated since 2013 so it may no longer be supported.
Another project called Reaver for Android or RFA has been out since 2013 and looks promising. Hopefully it will continue to be updated.
With all the projects out there the problem still is that most Smartphone’s do not have the correct chipset to do wireless hacking. One way to solve this is to use a USB compatible adapter / dongle the same way a PC would.
To do this a USB Host Mode OTG Cable is used to connect the micro USB to the standard USB adapter. This does work and a data capture can be done this way with a app called Pcap capture. The program will only currently use a 8187 chipset USB adapter.
The problem when using a standard USB adapter with a Smartphone is the five volts required to power the adapter. Some phones wont supply the power and a extra battery pack is needed to run the USB adapter.
The phones that can power a USB adapter will have a short battery life, sometimes as short as ten minutes.
Smartphones and developers are ever evolving, so there is no doubt things will change. But the current state of using a smart phone to do wireless penetration testing is not with us yet. Hopefully soon.